More than 1 Million Patients with Zoll Medical Were Exposed by Data Leak
Table of Contents
- By Steven
- Published: Mar 16, 2023
- Last Updated: Mar 16, 2023
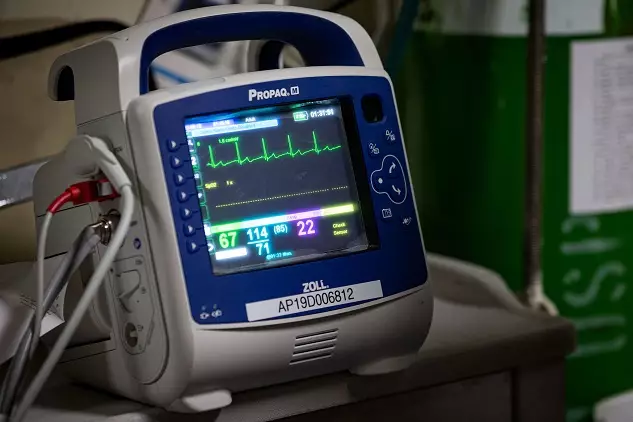
Zoll is a medical device and technologies company that offers its services to EMS, fire professionals, and rescuers. Even the U.S. Military relies on technologies from the company in order to save lives. Zoll recently suffered from a cyber attack that may have exposed over 1 million individuals. The attack happened fast and was coordinated by an unknown group, and we still don't have all the specific details yet.
How Did the Attack Occur?
On January 28, 2023, Zoll Medical detected strange activity on its data network. It appeared that unauthorized individuals were accessing the information on the network. There is no information about how the group was able to get into the data network, but they gained access to a large number of personal and health files. On February 2, 2023, the company began uncovering details about exactly what information was involved in the cyber attack and who was put at risk by it.
What Information Was Viewed or Stolen?
We don't know exactly what information was taken during the data breach, but Zoll suspects that some patients had their Social Security numbers, full names, addresses, and birth dates exposed by the attack. Until a full investigation is completed, we won't know exactly what information was shared, but anyone involved in the data breach should take steps to protect themselves from damage.
How Did Zoll Medical Admit to the Breach?
Zoll gave a statement to BusinessWire explaining that it was attacked and that some private health information may have been exposed by the attack. No ransomware group has admitted to coordinating this attack on Zoll, and the company itself hasn't offered a statement concerning whether it's paid a ransom or what is being done about the issue.
What Will Become of the Stolen Information?
The Zoll Medical information will likely be given away or sold online. Attackers could use the data to attempt fraudulent activities and to attempt to profit from it. We don't have any data showing the information has been used for fraudulent activities so far, but anyone exposed should take immediate steps to protect themselves.
What Should Affected Parties Do in the Aftermath of the Breach?
While we don't know that the attackers are leveraging the user data in a bad way, it's important to assume that they are. Zoll Medical sent notifications to approximately 1,004,443 patients, informing them they could have been exposed to the cyber attack. Anyone that's suspected of having been involved in being given complimentary access to Experian Identity Works for 24 months, but they have to sign up for the program still. If you receive a notice from Zoll, sign up to receive identity theft protection and leverage it to protect your assets. Also, watch your financial accounts closely and watch for suspicious activities. Zoll Medical is just one of many medical technology companies that have been attacked recently, and it's important to actively monitor and secure your information for that reason.
















